Cyber Security
Abstract
Cyber security entails the enhancement of diverse actions to shield the parts related to information technology. They are strategic issues involved in the formulation of cyber security policies that would enhance stability in information technology transfer. This calls for the formulation of policies that would shield the existing dangers related to cyber activities. These policies have defined steps that they take to enhance the development o cyber protection measures. These would help in the long run security of different systems.
Introduction
Cyber security is one of the most critical elements affecting communication networks in most Internet-providing institutions. The subject concerned with the development of cyber security issues focuses on the attempt to generate how different risks would accrue to individuals and other factors relating to cyber safety. However, some policies can apply in resolving the issues about cyber security. These policies provide different strategies for mitigating the network insecurity issues involved in different scenarios in the information technology sectors. These policies have not proved to be effective in diversified ways. The critiques can be attached to the existence of the already instituted security policies. Additionally, some recommendations may be applied in enhancing different sections affecting cyber security issues. Cyber security issues are critical and require appropriate development to enhance development in various information technology sectors.
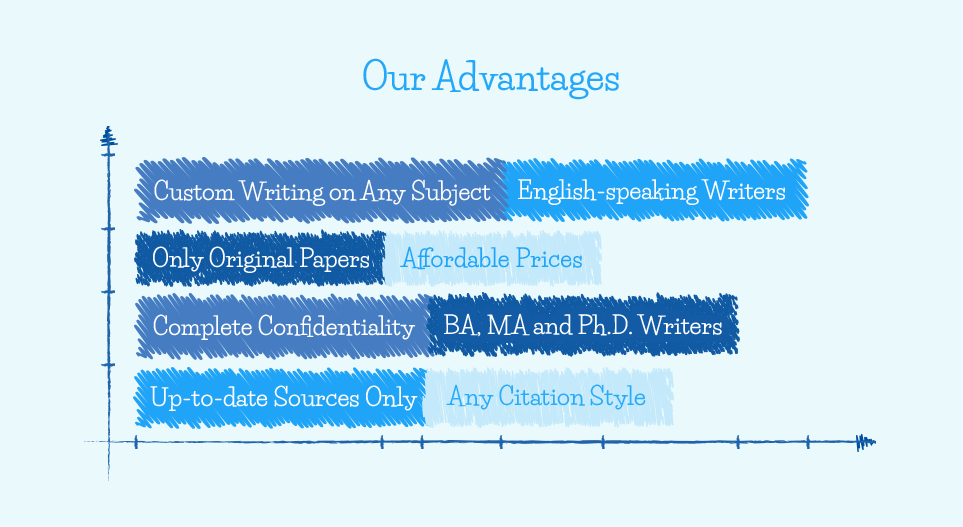
You can contact us if you want to Buy Cyber Essay help on this or any other topic.
Methodology
Several scholarly works have affected the research and studies concerning the impacts of the implementation of cyber security policies in different institutions. This study would centrally take the secondary sources in investigating the various aspects of cyber security policies in organizations. The peer-reviewed journals are some of the examples of the secondary sources that would be used in ensuring the development of the research work. The articles concerning the existence of threats and cyber security factors would also be beneficial in expounding the idea relevant for the subject of discussion.
Procedures for Establishing Cyber Security Policies
Some processes are followed in establishing the cyber security policies that have potential impacts on some stakeholders engaged in information technology. These procedures are elaborated in advance to provide a quality measure of enhancing policy formulation and organization in the cyber security field. These processes follow a concise way of enhancing policy development within the sector of cyber security. The following steps are instituted to identify the key strategies involved in cyber security policies.
Procedure One: Preliminary Evaluation
This is the first stage of cyber security procedures. This step involves the establishment of strategies for identifying the needs of the cyber security policies (Kabay & Kelley, 2009). It identifies some aspects of the policies involving computer users. This step implies an evaluation of the existing policies to see whether there are deficiencies about them given the activities of the existing cyber security policies. This process is meant to shed light on the effectiveness of the already existing policies. This measure attempts to explain the survey concerning the policies in reducing cyber security risks. This is also one of the most essential processes since it explains the need of having new policies in place. The central aim of this step is to scrutinize the existing policies to identify gaps that would trigger the need to establish a new policy. This step is one of the key factors that embrace the formation of other steps elaborating the existence of a need for a new cyber security policy. This point involves the collection of data that is responsible for the development of central reasons why the necessity to make changes in the system of security arose. The intentions of the data collection provide ideas related to some unique circumstances of data and privacy violations that people have experienced in operating the cyber items.
Procedure Two: Management Sensitization
Management is another essential aspect relating to the development of a cyber security policy. The consent of managers is important in gaining knowledge related to the development of cyber security measures. This implies that the awareness of the management concerning the development of a cyber security policy would be essential in establishing progress. The management approves the factors that are involved in the policies of cyber security. The management also reviews some of the issues of information technology involved in the policies (Beets & Raman, 2009). This adds to the credibility of the issues involved in developing key strategic policies that form cyber information security. At this stage, the management also provides some of the central ways of developing the sector’s certifications, which requires a certain public document. This stage is essential since it involves the manager’s opinion concerning a given policy.
Procedure Three: Need for Analysis
This is another essential stage of policy formulation in the cyber security sector. The working group in this sector is focused on the development of some strategic issues involved in the policy formulation. This implies that the working groups scrutinize the needs presented for redress to find appropriate needs that may require stronger protection with the new policies that the organizations intend to develop (Pacek, 2012). This need is appropriate in the development of security policies within the specified areas. This involves ranking the existing needs in a way that would promote the development of an appropriate address. The needs with large requirements are put under consideration within the organization. In this process, the opinions of all the groups within the enterprise are taken into account. In addition, this process involves the auditing of activities involved in the development of cyber security policies. This is an attempt to identify loopholes in some specific areas of the organization. This step aims at identifying the most essential needs that may put cyber security under different risks when in operation. This audit takes active scrutiny of the relationships of the organization and the stakeholders who affect the ways the policy formulation would use in a given priority.
Procedure Four: Policies and Procedures
At this stage, the working groups responsible for the scrutiny of cyber security needs will develop steps that would enhance the identification of specific policies that lead to the mitigation of the needs. This stage implies the identification of different policies that are anticipated to solve the cyber security needs involved in these circumstances. This step elaborates some of the existing options that would be available in solving the risk of security in case of a particular need. The relationship between the policies and the needs should be such that it enhances solutions to the needs. The working groups also develop strategies for developing the policies and procedures that facilitate the development of diverse security needs.
Procedure Five: Implementation
The implementation is one of the cumbersome stages of policy development in any organization. This step requires the acceptance of different groups to enhance development concerning security needs. At this point, there is an attempt to include the newly implemented policy into the operations of people within given organizations. This stage is complex since people have difficulty in adopting new policies. The security policies are put to test to enhance awareness (Kabay & Robertson, 2002). This part is also sensitive since it portrays how the implementers of the new policies would affect how the employees and other stakeholders embrace the security needs involved. Different groups are given direction on why they should accept the needs involved in the development of the new policies.
Procedure Six: Maintenance
Maintenance is the last step of developing the cyber security needs involved in the development of central policy measures. The formulated policies must be kept up to date to enhance the development of progress in terms of cyber security protection. This stage is also essential since it enhances key strategic issues involved in ensuring the security of the newly formulated policies. This stage also incorporates several facts in the development of central strategic issues as to the applying the newly formulated cyber security standards to the future period (Swartz, 2004). This step also includes the development of key issues involved in establishing awareness among given consumers. At this stage, it is important to identify the limiting factors that may lead to the poor performance of policies within the organization.
Effectiveness and Quality of Procedures involved in Developing Cyber Security Policies
Several factors within the formation of the policies would be subject to criticism. It is drawn from the scrutiny towards the effectiveness and quality of procedures involved in the formulation of cyber security policies (Bosworth, Kabay & Whyne, 2009). One of the critiques affecting how the cyber security policies are formed is about how information is collected about an existing need. This process has failed to embrace universality in the policy formulation strategies. This also implies that the standards that would be formed affect how the policies would relate to the existing policies. One of the problems that cyber security systems face is the lack of universal policies that would enhance appropriate global security. For example, the preliminary evaluation stage involves finding needs that would be responsible for a given organization. This fact implies that the findings would only serve some part of the organization. This idea does not embrace universality that would enhance stable cyber security measures. The fact that the need for new cyber security policies depends on different organizations would mean that there are failures in an attempt to develop universal procedures of mitigating the global cyber security policies.
The procedures involved do not embrace some given levels of practicality. For example, procedures are general and affect how the quality of the outcome would be obvious once the new policies are formulated. In the implementation stage, there is no clear outlay on which groups of people would be affected by the new cyber security policies. This leaves a loose end to how the implementation of new policies would take place in various scenarios (Bennett, 2012). This has a high risk of poor evaluation of issues that pertain to cyber security. The issues involved in the implementation of cyber security would be effective if specified groups would be identified to solve the issues limiting their abilities to adopt the new cyber security policies.
There are no detailed explanations with regards to the steps involved in keeping the new cyber security policies to work better inappropriate ways. The steps give a general guide to how the maintenance workgroups would look onto strategies of enhancing the freshness and adequacy of the policies involved in mitigating the cyber security risks. Lack of clear guidelines on how to make the maintenance extra appealing for adaptation would affect how proper cyber security measures take place. Lack of a detailed explanation of how to perform this section may lead to a lack of existing directions in identifying policies related to cyber security maintenance.
Recommendations
Some recommendations can be applied in the development of key issues of cyber security policies. One of the recommendations involves the identification of universal ways of establishing research by performing global surveys instead of enhancing the organization-based practices. These facts are involved in the development of an appropriate strategy that would enhance the development of universal cyber security standards. This element identifies some of the global concerns towards cyber security needs within the global hemisphere. This strategy of developing a universal measure of identifying needs for new policies would ensure that there are no looming threats to the existing users of information technology within given sectors.
How it works
Step 1
Visit our website and go to the order formStep 2
Fill in specific essay details in your order description sectionStep 3
Pay for your custom essay and get your order verifiedStep 4
Process of writing your academic assignmentStep 5
Editing and anti-plagiarism checkStep 6
On-time delivery of an already written essayAnother recommendation is the identification of key strategic issues involved in maintaining the various cyber security policies involved in the procedures (UMUC, 2011). This may take place by categorizing the policies depending on how it affects the development of sound policies. There are many policies related to cyber security. For example, some policies affect data protection within the cyber security sector. To identify key strategic issues involved in the maintenance of new policies, the different cyber security fields should be identified. This accuracy would pertain to the identification of parties that would be affected by the newly formulated cyber policies.
Other issues experienced in the procedures include the generalization of ideas involved in developing appropriate security measures. To mitigate such problems, there are ways in which a detailed explanation can be provided to facilitate the specificity of facts. Cyber security affects different dimensions of information technology. The procedure of formulating the new policies should emphasize singling out some specific characteristics involved in developing appropriate levels of security policies. This idea only focuses on narrowing down the security requirements involved in explaining different cyber security policies. This would also give clear guidelines for the policy writers who attempt to integrate the new policies with the existing cyber security standards.
Cyber Security Threats in the USA
In the United States of America, some aspects of threats relating to cyber security would compromise the smooth running of plans within the nation. One of the central factors relating to threats within the USA security system is cyber warfare (OConnell, 2012). This involves hacking of particular systems to facilitate sabotage and espionage elements connected with political issues. It is a common threat affecting the United States due to the looming interests that have been developed in the political arena. The political field has become sensitive due to the existing interests that people attach to the political status of the USA. This has motivated the practices of espionage and sabotage to gain an upper hand in political practices.
There is a threat of using the information to achieve certain strategic goals involved in the US national security system (Streater, 2010). The development of these attacks has even bypassed terrorism that is no longer considered an ultimate cause of threats in the development. Cyber threats in the USA have been applied in performing miscalculations related to the development of key strategic issues in the development of the nation. This threat of invading the systems is a threat to the stability of the development of the nation.
Conclusion
Cyber security involves the development of different measures to shield the sectors related to information technology. There are strategic issues involved in the formulation of cyber security policies that would enhance stability in information technology transfer. These policies have some inefficiency that pulls behind their extent of operations. Such ineffectiveness can be mitigated by developing adequate universality issues involved in stable cyber security measures.
Cyber Security